The Problems:

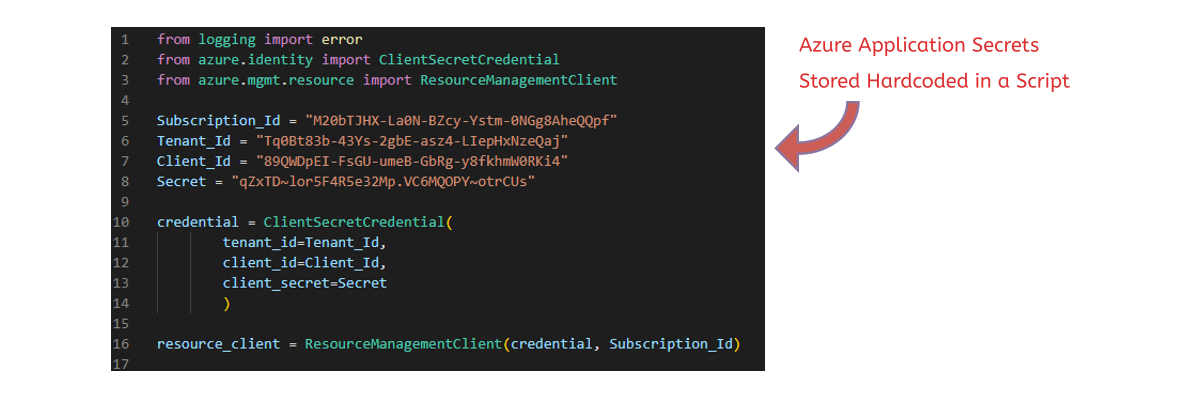
- Industry Standard to Store Access Keys in Plaintext
- Cloud Providers Instructing Administrators to Do This
- Other Methods of Secure Key Storage are Too Complex
- Secrets are Stored Hardcoded in Scripts and Applications
- Secure Development Practices are Not Always Enforced
- Secrets and Access Keys Exposed in Web Application Code

Why Are We Making It Even Easier for Attackers?
The Solutions:

Enhanced Multi-Factor Authentication Methods Attached to Access Keys

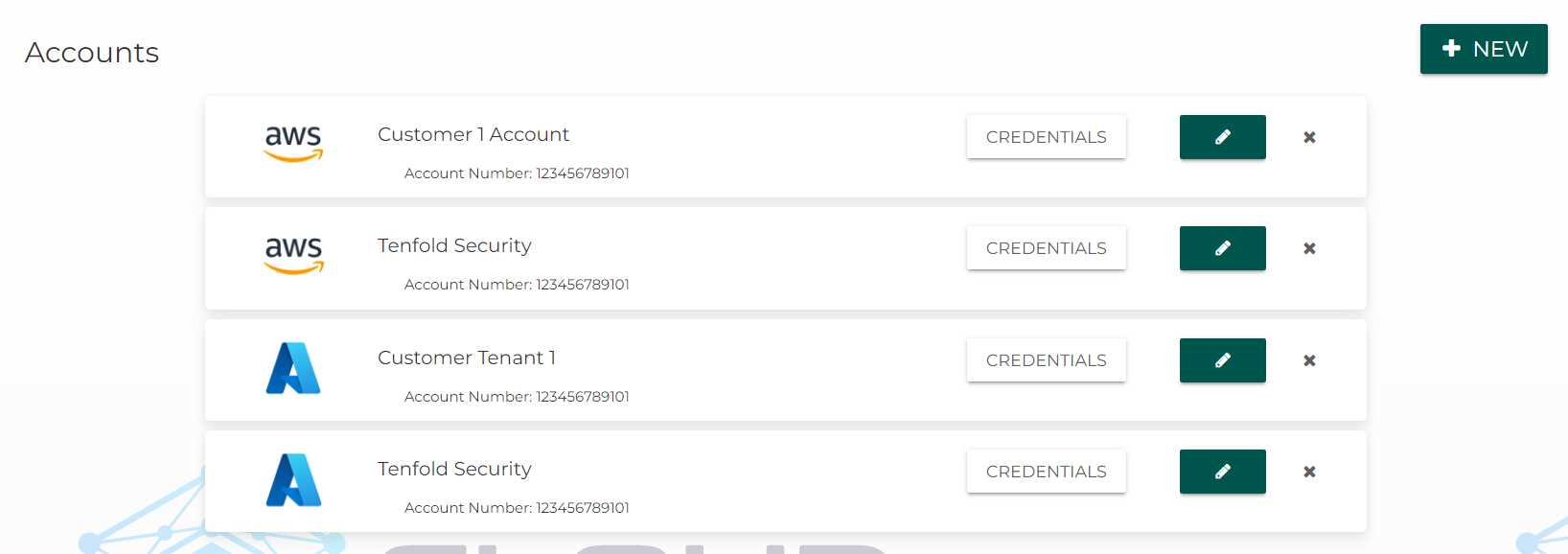
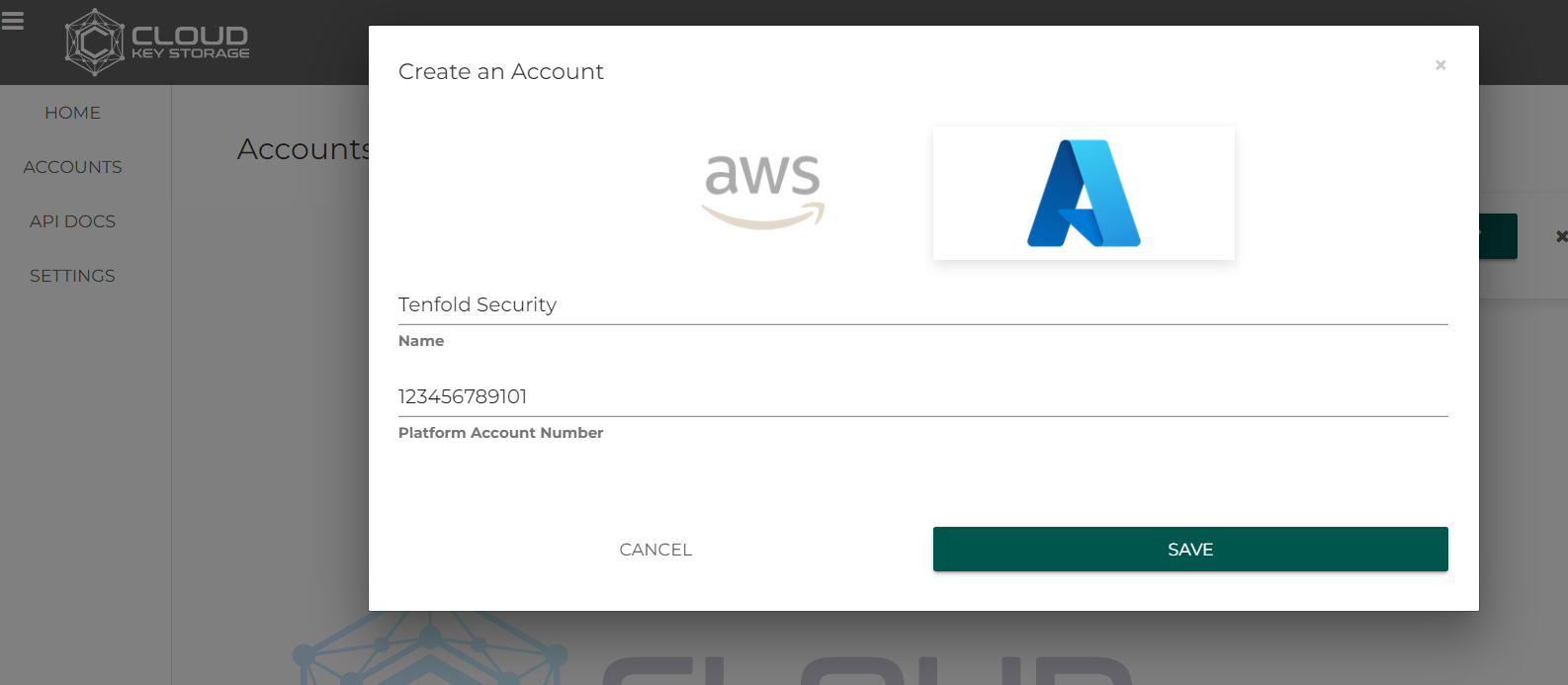
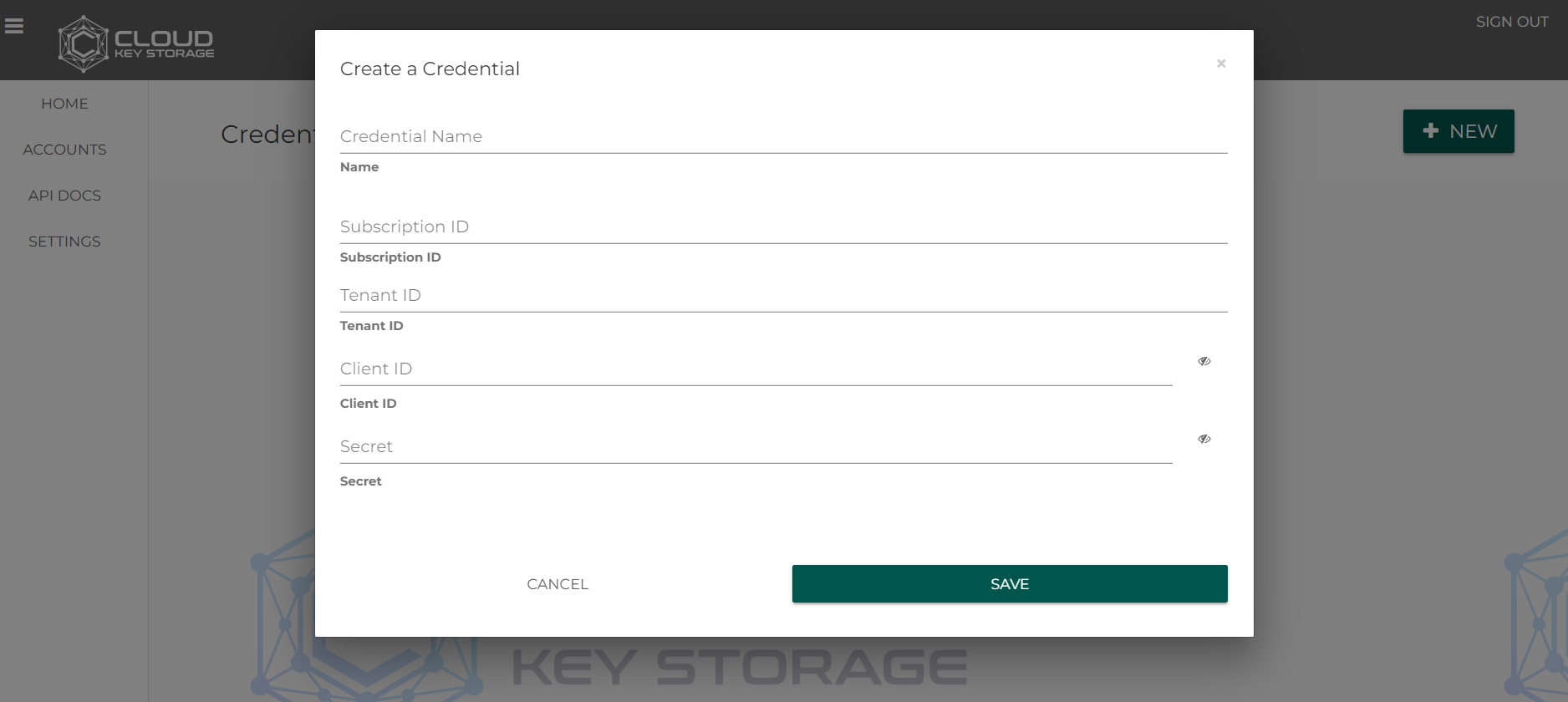
Storage for Multiple Cloud Providers Like AWS and Azure

Enhanced Tracking and Usage of Secrets and Access Keys

Secrets and Keys Stored w/ Military Grade Encryption